Read this article in 日本語.
Let’s get this one clear at the outset. A major factor for security is not to allow other software to intercept network connections. Typically, this includes antivirus, parental control, and debugging software.
These tools think they are doing it for a good reason, but there are better ways for them to operate such as an extension which uses the Chromium network (e.g. webRequest) APIs. In the case of an antivirus product, the product can still protect the computer from malicious downloads by scanning downloaded files.
How it works
What happens is that the products install a new root certificate on the computer, and when the browser tries to connect to a secure website, the software intercepts the connection, connects to the website itself, and proxies the connection to the browser, decrypting and scanning the data, then signing the browser connection with its own certificate. As a result, the browser is unable to control the security of the connection to the website – it cannot check EV certificates, it cannot ensure that high-grade ciphers are used, it cannot check for blacklisted or revoked certificates, and it cannot ensure that the website really is the website that it is supposed to be.
Browsers such as Vivaldi are extremely good at doing all of the above and are usually super fast at responding to changes in cipher technology, and certificate incidents. The browser needs to be allowed to control this.
More concerns over attacker misuse
To make it worse, when an application installs a new root certificate, it means that anyone else with access to that private root certificate can create fake versions of secure websites, and the computer will trust them and think they are the real website. If the intercepting software uses the same signing certificate for all installations – a common mistake – this allows an attacker to use their copy of the certificate to intercept and sign your connections.
Some apps claim that intercepting network connections allows them to detect when a website tries to exploit a known vulnerability in the browser to install malware.
Vivaldi protection
In reality, the Chromium engine used by Vivaldi has sandbox protection built in which minimizes the impact of such issues. Chromium is updated frequently, and the response to security issues is very fast, so users normally have a patch installed before an antivirus product has a chance to issue an update to detect an attack. Often, when a product claims to have detected such an attack, it’s an attack aimed at an outdated browser rather than Vivaldi, and the attack would not have succeeded anyway. Even so, by using the network or webRequest API, the product could still offer protection without intercepting connections.
Intercepting connections is just a bad approach and we do not recommend allowing software to intercept connections.
Stay tuned for more tips in our series on privacy and security.
* * *
Read more blog posts from the series:
- The basics of web browser security: an introduction
- Shared networks, tracking and fingerprinting
- Website permissions and third-party services in Vivaldi
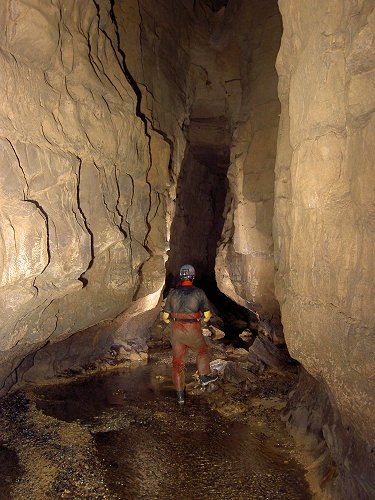
Main photo by Nicolas Tissot on Unsplash.